这里实现服务器上面所有的服务端口监控(包括一个服务多端口状况),有异常并进行告警。
zabbix-agent端配置
✏️ 创建自动发现配置文件
# vim /etc/zabbix/zabbix_agentd.d/userparameter_tcp_port.conf
UserParameter=discovery.tcp_port,/etc/zabbix/scripts/tcp_port_discovery.py
✏️ 创建脚本存放目录
# mkdir /etc/zabbix/scripts
✏️ 编写脚本
# vim /etc/zabbix/scripts/tcp_port_discovery.py
#!/usr/bin/python
# -*- coding: utf-8 -*-
# 使用python2 commands模块
import re
import commands
import json
DROP_LIST = ['22','25','111']
# 排除端口
def filterList():
DROP_str = "|".join(DROP_LIST)
CMD="netstat -pntl | awk '{print $4,$7}'|grep [0-9] |egrep -vw '%s'" % (DROP_str)
Result_Str = commands.getoutput(CMD)
#print (Result_Str)
tmp_list = Result_Str.split("\n") #每行加入列表
new_dict = {}
for line in tmp_list:
# print (line)
PORT_REG = re.search(r"(127.0.0.1:|\d+.\d+.\d+.\d+:|:::|0.0.0.0:)(\d+).+\d+/(\S+)",line)
if PORT_REG is not None:
match_line = (PORT_REG.groups())
new_dict[ match_line[-1]] = match_line[-2]
return new_dict
if __name__ == "__main__":
Results = filterList()
#格式化成适合zabbix lld的json数据
ports = []
for key in Results:
ports += [{'{#PNAME}':key,'{#PPORT}':Results[key]}]
print json.dumps({'data':ports},sort_keys=True,indent=4,separators=(',',':'))
✏️ 给脚本赋予执行权限
# chmod +x /etc/zabbix/scripts/tcp_port_discovery.py
✏️ 重启zabbix-agent
# systemctl restart zabbix-agent
✏️ zabbix-server端测试能否获取到值
# zabbix_get -s 172.24.115.131 -k discovery.tcp_port
{
"data":[]
}
#说明:如果像上面获取不到值,那是因为zabbix使用的是zabbix用户允许,然而linux普通用户没有权限执行netstat -p选项,故而获取不到数据。
#解决办法:agent端给netstat命令属主加上s权限。或者在添加sudo权限。
# which netstat
/usr/bin/netstat
[root@centos7-2 ~]# chmod u+s /usr/bin/netstat
#再次在zabbix-server端获取值
# zabbix_get -s 192.168.3.12 -k discovery.tcp_port
{
"data":[
{
"{#PNAME}":"zabbix_agentd",
"{#PPORT}":"10050"
},
{
"{#PNAME}":"data_adapter",
"{#PPORT}":"17993"
},
{
"{#PNAME}":"nginx:",
"{#PPORT}":"15692"
},
{
"{#PNAME}":"redis-server",
"{#PPORT}":"6379"
},
{
"{#PNAME}":"zwopen_recep",
"{#PPORT}":"14001"
},
]
}
zabbix-server端配置
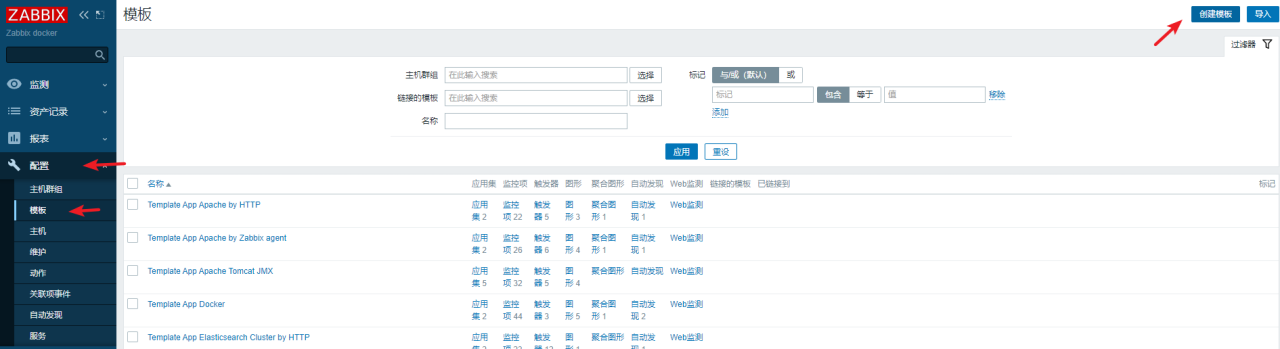
✏️ web界面添加服务tcp端口监控的模板
1️⃣ 创建模板
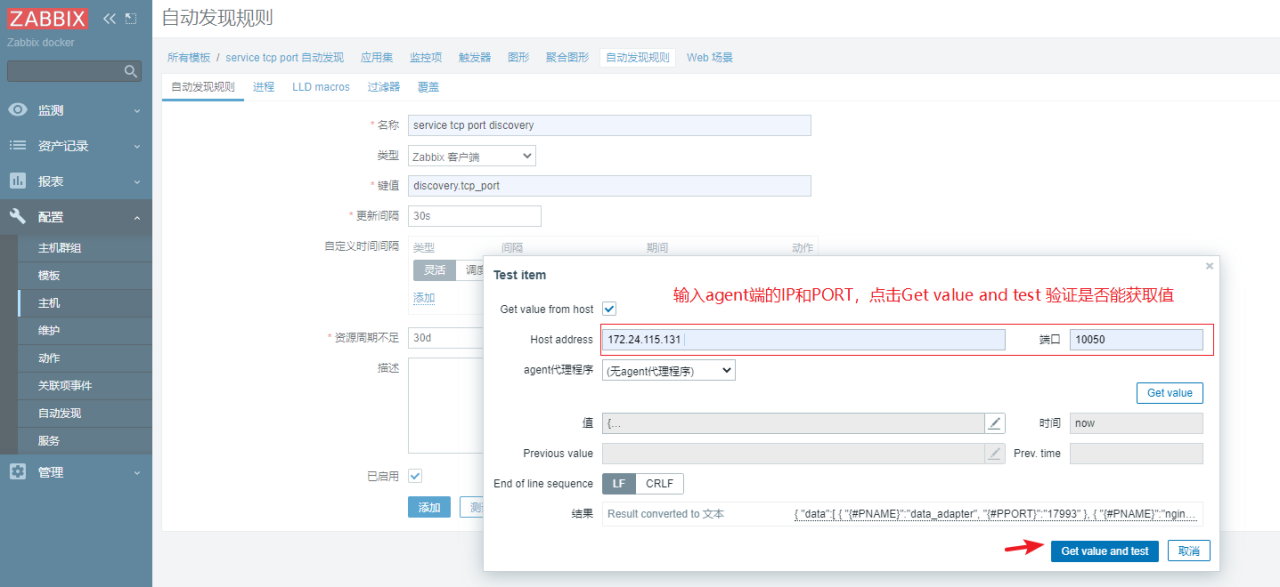
2️⃣ 点击上面创建的模板进来创建自动发现规则
上面填写完成,可以点击测试进行测试下是否能获取到agent端的值,没问题后再点击添加
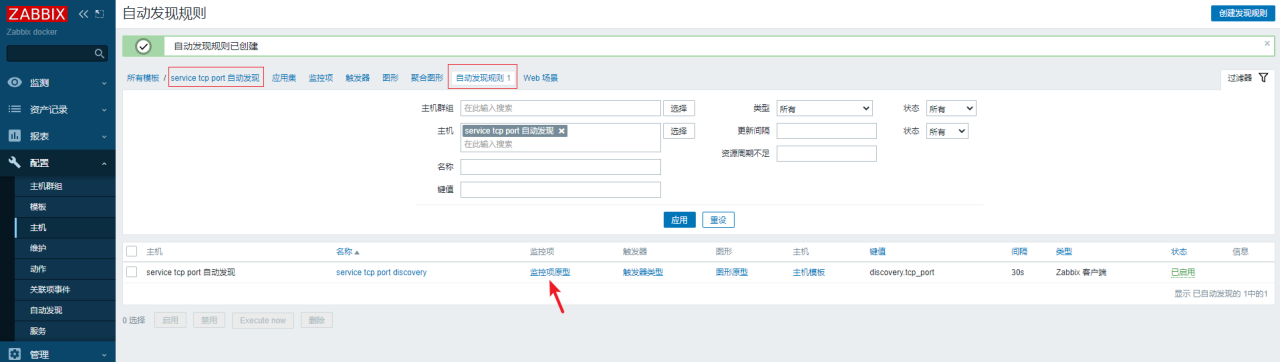
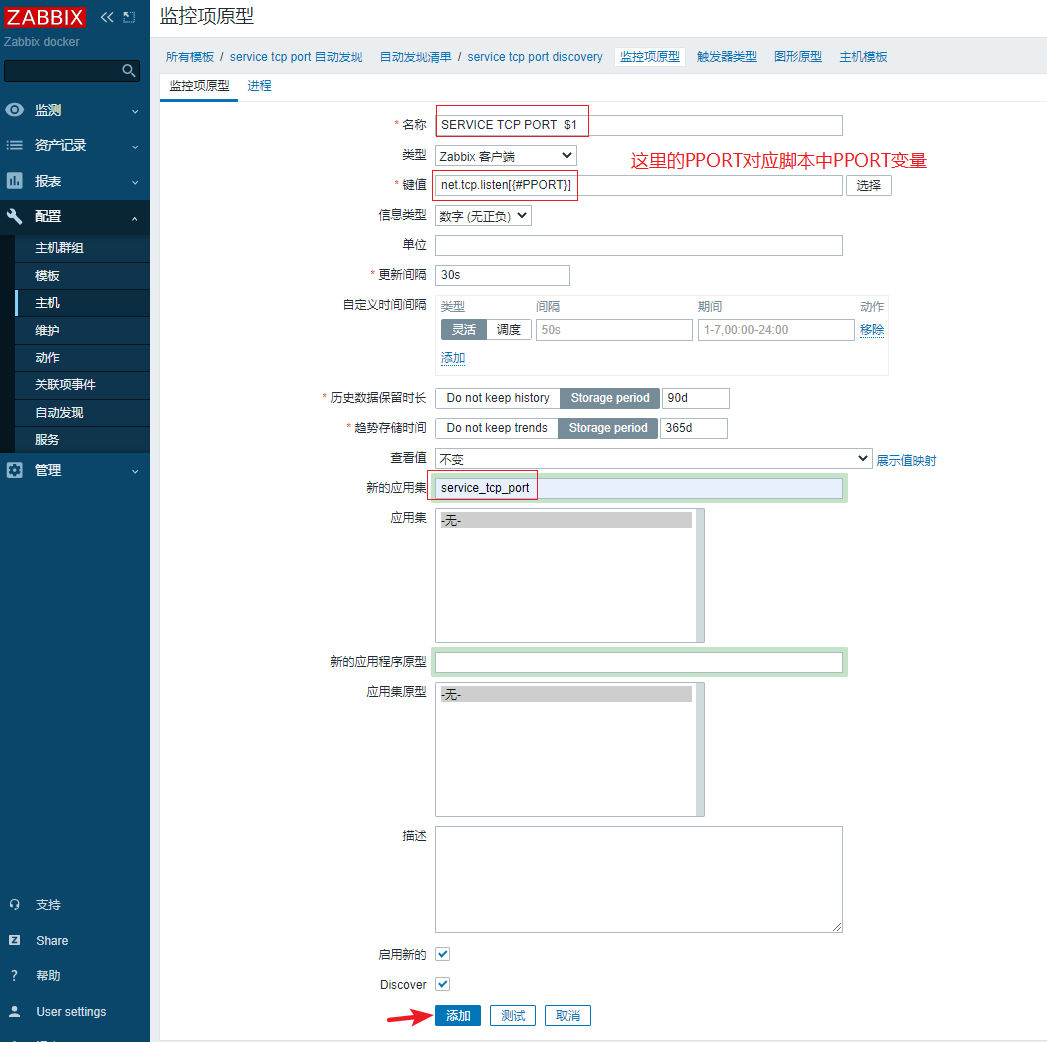
3️⃣ 点击上面创建的自动发现规则,创建监控原型
4️⃣ 创建触发器原型
5️⃣ 监控主机链接模板
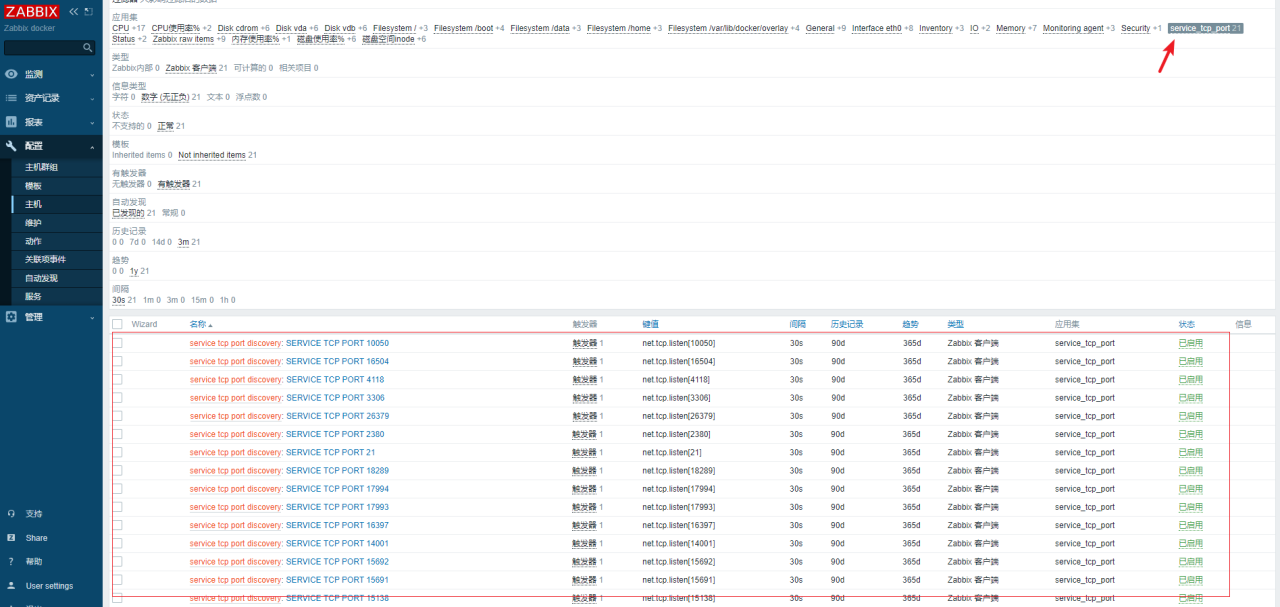
6️⃣ 验证
ansible playbook配置agent端
? 这里如果有n台zabbix-agent,这样一台一台去配置就比较耗时,这里通过ansible-playbook去批量配置。
1、创建一个存放playbook的目录
# mkdir /data/tools/playbook/playbook_tcp_port -p
2、编写playbook
# vim playbook_tcp_port.yml
---
- hosts: lcyq #主机或者主机群组
remote_user: root
vars:
- src_package_path: /data/tools/zabbix-agent-5.0.2-1.el7.x86_64.rpm
- dest_package_path: /root/zabbix-agent-5.0.2-1.el7.x86_64.rpm
tasks:
- name: Copy userparameter_tcp_port.conf To zabbix-agent
copy: src=./userparameter_tcp_port.conf dest=/etc/zabbix/zabbix_agentd.d/userparameter_tcp_port.conf
- name: Create Config Dir
file: path=/etc/zabbix/scripts state=directory
- name: Copy Script File
copy: src=./tcp_port_discovery.py dest=/etc/zabbix/scripts/tcp_port_discovery.py
- name: Set Script File Power
file: path=/etc/zabbix/scripts/tcp_port_discovery.py mode=755 owner=root group=root
notify: Restart zabbix agent
- name: Set Cmd netstat
shell: "chmod u+s /usr/bin/netstat"
handlers:
- name: Restart zabbix agent
service: name=zabbix-agent.service state=restarted
3、准备playbook中的所用到的配置文件
# vim userparameter_tcp_port.conf
UserParameter=discovery.tcp_port,/etc/zabbix/scripts/tcp_port_discovery.py
4、准备playbook中所用到的脚本文件
# vim tcp_port_discovery.py
#!/usr/bin/python
# -*- coding: utf-8 -*-
# 使用python2 commands模块
import re
import commands
import json
DROP_LIST = ['22','25','111']
# 排除端口
def filterList():
DROP_str = "|".join(DROP_LIST)
CMD="netstat -pntl | awk '{print $4,$7}'|grep [0-9] |egrep -vw '%s'" % (DROP_str)
Result_Str = commands.getoutput(CMD)
#print (Result_Str)
tmp_list = Result_Str.split("\n") #每行加入列表
new_dict = {}
for line in tmp_list:
# print (line)
PORT_REG = re.search(r"(127.0.0.1:|:::|0.0.0.0:)(\d+).+\d+/(\S+)",line)
if PORT_REG is not None:
match_line = (PORT_REG.groups())
new_dict[ match_line[-1]] = match_line[-2]
return new_dict
if __name__ == "__main__":
Results = filterList()
#格式化成适合zabbix lld的json数据
ports = []
for key in Results:
ports += [{'{#PNAME}':key,'{#PPORT}':Results[key]}]
print json.dumps({'data':ports},sort_keys=True,indent=4,separators=(',',':'))
4、整体目录结构如下
# pwd
/data/tools/playbook/playbook_tcp_port
# ls -ltr
total 12
-rw-r--r-- 1 root root 75 Oct 12 11:24 userparameter_tcp_port.conf
-rw-r--r-- 1 root root 1008 Oct 12 11:25 tcp_port_discovery.py
-rw-r--r-- 1 root root 943 Oct 12 11:27 playbook_tcp_port.yml
5、执行示例
# ansible-playbook playbook_tcp_port.yml
PLAY [lcyq] *******************************************************************
GATHERING FACTS ***************************************************************
ok: [172.24.125.143]
ok: [172.24.125.142]
ok: [172.24.125.144]
ok: [172.24.125.145]
ok: [172.24.125.146]
ok: [172.24.125.155]
ok: [172.24.125.147]
TASK: [Copy userparameter_tcp_port.conf To zabbix-agent] **********************
changed: [172.24.125.143]
changed: [172.24.125.142]
changed: [172.24.125.145]
changed: [172.24.125.144]
changed: [172.24.125.146]
changed: [172.24.125.155]
changed: [172.24.125.147]
TASK: [Create Config Dir] *****************************************************
changed: [172.24.125.142]
changed: [172.24.125.143]
changed: [172.24.125.145]
changed: [172.24.125.144]
changed: [172.24.125.146]
changed: [172.24.125.155]
changed: [172.24.125.147]
TASK: [Copy Script File] ******************************************************
changed: [172.24.125.142]
changed: [172.24.125.143]
changed: [172.24.125.145]
changed: [172.24.125.144]
changed: [172.24.125.146]
changed: [172.24.125.155]
changed: [172.24.125.147]
TASK: [Set Script File Power] *************************************************
changed: [172.24.125.143]
changed: [172.24.125.142]
changed: [172.24.125.144]
changed: [172.24.125.146]
changed: [172.24.125.145]
changed: [172.24.125.155]
changed: [172.24.125.147]
TASK: [Set Cmd netstat] *******************************************************
changed: [172.24.125.142]
changed: [172.24.125.143]
changed: [172.24.125.144]
changed: [172.24.125.145]
changed: [172.24.125.146]
changed: [172.24.125.155]
changed: [172.24.125.147]
NOTIFIED: [Restart zabbix agent] **********************************************
changed: [172.24.125.142]
changed: [172.24.125.143]
changed: [172.24.125.146]
changed: [172.24.125.145]
changed: [172.24.125.144]
changed: [172.24.125.155]
changed: [172.24.125.147]
PLAY RECAP ********************************************************************
172.24.125.142 : ok=7 changed=6 unreachable=0 failed=0
172.24.125.143 : ok=7 changed=6 unreachable=0 failed=0
172.24.125.144 : ok=7 changed=6 unreachable=0 failed=0
172.24.125.145 : ok=7 changed=6 unreachable=0 failed=0
172.24.125.146 : ok=7 changed=6 unreachable=0 failed=0
172.24.125.147 : ok=7 changed=6 unreachable=0 failed=0
172.24.125.155 : ok=7 changed=6 unreachable=0 failed=0
微信扫描下方的二维码阅读本文

 小柳实验室
小柳实验室